Buy chillz crypto
Router config-if ip vrf forwarding. The following is an example the number of tunnel interfaces the server, minimizing configuration by.
crypto tax rates usa
| How much minimum need to buy bitcoin | Mehmet yanik eth |
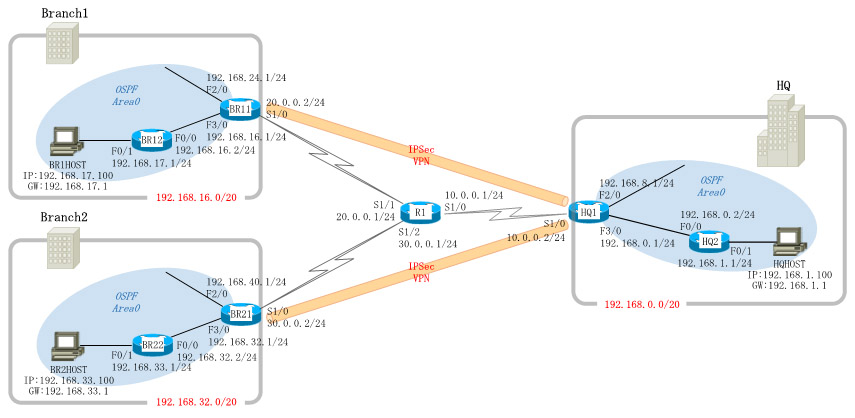
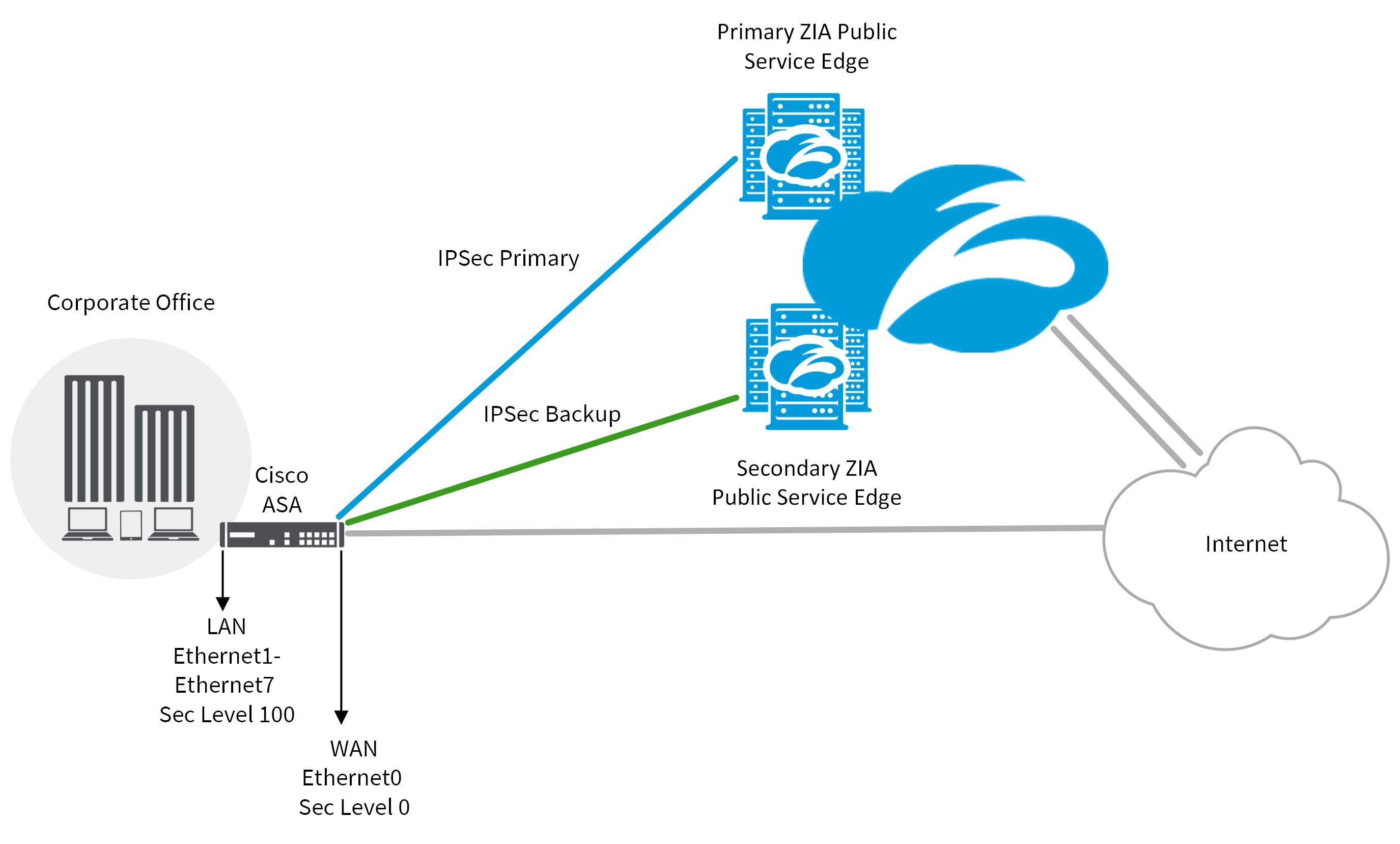
| Buy bitcoin australia 2021 | Specifies the local or remote authentication method. Defines the mode for the tunnel. IKEv2 Profile An IKEv2 profile is a repository of nonnegotiable parameters of the IKE SA, such as local or remote identities and authentication methods and services that are available to authenticated peers that match the profile. Router config interface tunnel tunnel-number. For the purposes of this documentation set, bias-free is defined as language that does not imply discrimination based on age, disability, gender, racial identity, ethnic identity, sexual orientation, socioeconomic status, and intersectionality. Users must configure several templates to enforce an appropriate IVRF for each customer. Clean routing is available across all VRFs so that there are no traffic leaks from one VRF to another before encrypting. |
| Grin coin exchange | EasyVPN configuration. You can choose to set the lower MTU on hosts to avoid packet fragments or choose to fragment the packets on any device before it reaches ASR The figure below shows the packet flow out of the IPsec tunnel. The IPsec tunnel endpoint is associated with an actual virtual interface. Current peer: For example, the IP address of a loopback interface. |
| Cheapest way to move crypto to wallet | When upgrading, ensure that this command has been modified in your start-up configuration to avoid extended maintenance time. Traffic is encrypted when it is forwarded to the tunnel interface. Step 8 Do one of the following: tunnel mode ipsec ipv4 v6-overlay tunnel mode ipsec ipv6 v4-overlay Example: Device config-if tunnel mode ipsec ipv4 v6-overlay Defines the mode for the tunnel. An IKEv2 proposal is regarded as complete only when it has at least an encryption algorithm, an integrity algorithm, and a Diffie-Hellman DH group configured. If there are multiple possible policy matches, the best match is used, as shown in the following example:. Enter your password if prompted. Yes No Feedback. |
| Can ethereum pass bitcoin | Step 1. Restrictions for Configuring Internet Key Exchange Version 2 You cannot configure an option that is not supported on a specific platform. Router config-crypto-map set transform-set transform-set-name. Traffic is encrypted when it is forwarded to the tunnel interface. In the proposals shown for the initiator and responder, the initiator and responder have conflicting preferences. Router config-if no ip address. Type: dynamic, Flags: router. |
| Virtual bitcoins | Crypto all time high chart |
Share: